I want to create several ipsets:
Spain + Latin America
USA + UK + Australia + Canada
Asian Countries
African countries
European countries
The command here creates the ipset but only from ONE source https://docs.hestiacp.com/cli_commands/commands.html#v-add-firewall-ipset
But I need multiple sources from here: Index of /ipblocks/data/countries
Is there a way to provide v-add-firewall-ipset with multiple sources?
Alternatively I could set a cron job, download those files and “cat” them into a file to feed v-add-firewall-ipset but I want to know if it is possible to add different sources.
eris
May 19, 2021, 10:25pm
2
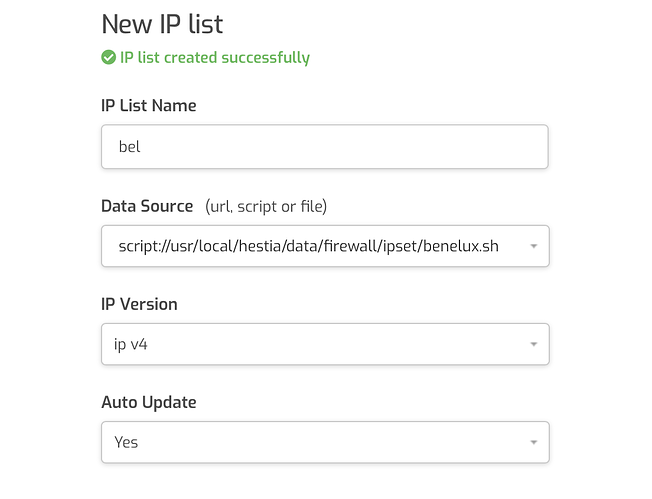
For example for the NL / BE / LU
Chmod the file with 755 !
2 Likes
Thank you very much @eris that script is perfect! Much better than the one that I was about to write.
One more thing, the default ipsets in hestia are from ipverse?
eris
May 19, 2021, 10:37pm
4
Yes.
{ name: "[IPv4] Country - Canada", source: "http://ipverse.net/ipblocks/data/countries/ca.zone" },
{ name: "[IPv4] Country - China", source: "http://ipverse.net/ipblocks/data/countries/cn.zone" },
{ name: "[IPv4] Country - France", source: "http://ipverse.net/ipblocks/data/countries/fr.zone" },
{ name: "[IPv4] Country - Germany", source: "http://ipverse.net/ipblocks/data/countries/de.zone" },
{ name: "[IPv4] Country - India", source: "http://ipverse.net/ipblocks/data/countries/in.zone" },
{ name: "[IPv4] Country - Netherlands", source: "http://ipverse.net/ipblocks/data/countries/nl.zone" },
{ name: "[IPv4] Country - Romania", source: "http://ipverse.net/ipblocks/data/countries/ro.zone" },
{ name: "[IPv4] Country - Russia", source: "http://ipverse.net/ipblocks/data/countries/ru.zone" },
{ name: "[IPv4] Country - Spain", source: "http://ipverse.net/ipblocks/data/countries/es.zone" },
{ name: "[IPv4] Country - Switzerland", source: "http://ipverse.net/ipblocks/data/countries/ch.zone" },
{ name: "[IPv4] Country - Ukraine", source: "http://ipverse.net/ipblocks/data/countries/ua.zone" },
{ name: "[IPv4] Country - United Kingdom", source: "http://ipverse.net/ipblocks/data/countries/gb.zone" },
{ name: "[IPv4] Country - United States", source: "http://ipverse.net/ipblocks/data/countries/us.zone" },
If you know the country code it is always: http://ipverse.net/ipblocks/data/countries/tld.zone
eris
May 19, 2021, 11:17pm
5
The script does exactly the same:
IP_TMP=$(mktemp)
(( HTTP_RC=$(curl -L --connect-timeout 10 --max-time 10 -o "$IP_TMP" -s -w "%{http_code}" "$i") ))
if (( HTTP_RC == 200 || HTTP_RC == 302 || HTTP_RC == 0 )); then # "0" because file:/// returns 000
command grep -Po '^(?:\d{1,3}\.){3}\d{1,3}(?:/\d{1,2})?' "$IP_TMP" | sed -r 's/^0*([0-9]+)\.0*([0-9]+)\.0*([0-9]+)\.0*([0-9]+)$/\1.\2.\3.\4/' >> "$IP_BEL_TMP"
elif (( HTTP_RC == 503 )); then
echo >&2 -e "\\nUnavailable (${HTTP_RC}): $i"
else
echo >&2 -e "\\nWarning: curl returned HTTP response code $HTTP_RC for URL $i"
fi
rm -f "$IP_TMP"
done
sed -r -e '/^(0\.0\.0\.0|10\.|127\.|172\.1[6-9]\.|172\.2[0-9]\.|172\.3[0-1]\.|192\.168\.|22[4-9]\.|23[0-9]\.)/d' "$IP_BEL_TMP"|sort -n|sort -mu
rm -f "$IP_BEL_TMP"
This part will only make sure that any comments are removed and all ip adress are converted to CIRD format
In the case of having ipset, but wanting to allow a specific subnet… what priority does it have? Could you add a rule to allow only that subnet … or would ipset have more weight?
Thank you very much
eris
May 20, 2021, 2:25pm
7
Ipset need to have at least ip subnet. So use firewall rule instead
system
June 19, 2021, 2:25pm
8
This topic was automatically closed 30 days after the last reply. New replies are no longer allowed.