Hi,
Today, March 18h, 2026 has been released Roundcube 1.6.14 and it fixes eight security vulnerabilities.
Security fixes
- Fix pre-auth arbitrary file write via unsafe deserialization in redis/memcache session handler, reported by y0us.
- Fix bug where a password could get changed without providing the old password, reported by flydragon777.
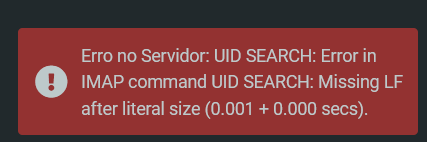
- Fix IMAP Injection + CSRF bypass in mail search, reported by Martila Security Research Team.
- Fix remote image blocking bypass via various SVG animate attributes, reported by nullcathedral.
- Fix remote image blocking bypass via a crafted body background attribute, reported by nullcathedral.
- Fix fixed position mitigation bypass via use of !important, reported by nullcathedral.
- Fix XSS issue in a HTML attachment preview, reported by aikido_security.
- Fix SSRF + Information Disclosure via stylesheet links to a local network hosts, reported by Georgios Tsimpidas (aka Frey), Security Researcher at https://i0.rs/.
More info about the release:
I’ve created this PR to bump Roundcube version to 1.6.14:
If you want to update Roundcube now, you can do it manually using below steps.
Disclaimer: it should work fine BUT use this procedure at your own risk!
Note: I assume your Roundcube current installed version is 1.6.13.
0.- BACKUP, always backup… just in case ![]()
Note: If you use MySQL instead of MariaDB, replace mariadb-dump with mysqldump.
mariadb-dump --defaults-file=/usr/local/hestia/conf/.mysql.localhost --single-transaction --routines -B roundcube > /tmp/roundcube_1.6.13.sql
tar zcf /tmp/roundcube_1.6.13_backup_before_upgrade_1.6.14.tar.gz /etc/roundcube /var/lib/roundcube /tmp/roundcube_1.6.13.sql
rm /tmp/roundcube_1.6.13.sql
Now save to another place the backup file located here /tmp/roundcube_1.6.13_backup_before_upgrade_1.6.14.tar.gz
Example:
mv /tmp/roundcube_1.6.13_backup_before_upgrade_1.6.14.tar.gz /backup/
1.- Modify upgrade.conf file so the Roundcube version is 1.6.14 instead of 1.6.13:
sed -E -i "s/^rc_v='1.*/rc_v='1.6.14'/" /usr/local/hestia/install/upgrade/upgrade.conf
2.- Upgrade roundcube using below Hestia’s command. It will detect that roundcube is installed, will detect the new version and will update it:
If you have disabled php functions system and proc_open in PHP CLI, you won’t receive errors but Roundcube won’t update to version 1.6.13, it will remain in version 1.6.11 so to avoid this problem, before continue, remove both functions for your current PHP CLI version. These two commands will remove the functions from your current PHP CLI version (version is detected automatically).
sed -i -E 's/(^disable_functions.*),proc_open(.*$)/\1\2/' /etc/php/$(php -v | head -n1 | grep -o '[0-9]\.[0-9]')/cli/php.ini
sed -i -E 's/(^disable_functions.*),system(.*$)/\1\2/' /etc/php/$(php -v | head -n1 | grep -o '[0-9]\.[0-9]')/cli/php.ini
Now you can proceed with the upgrade;
v-add-sys-roundcube
3.- Update composer packages used by roundcube:
cd /var/lib/roundcube/
COMPOSER_ALLOW_SUPERUSER=1 composer -n update
If composer is not in your path, you should use the full path to composer utility, if you don’t know even whether you have it installed or how to install it, just install it for admin user.
v-add-user-composer admin
If it is not installed, the command will install it for the admin user and if you had it already installed, you will be informed. So, now that it is installed you can update composer packages using the full path to composer.
cd /var/lib/roundcube/
COMPOSER_ALLOW_SUPERUSER=1 /home/admin/.composer/composer -n update
Hope it helps. Take care.