Hi
Is strenghening the security of Nginx using ModScurity 3 and OWASP rules somewhere in a roadmap?
Or is this topic to dubious?
N.
Hello @neven, I’m interested in modsecurity and have been thinking on adding it into Hestiacp but it isn’t on our roadmap currently.
Unfortunately I don’t know any official modsecurity ppa so we would have to ship and maintain a precompiled package more regularly than our usual release cycle.
I have a test server with ubuntu and hestiaCP 1.1.0 beta installation. Will try to compile libmodscecurity over the weekend and automate owasp updates there.
Server is at test.vinsdigital.com. I can give you a sudoer if you want. Msg me. I’m currently using it to test 1.1.0 quick deploy features. Will post bugs, comments, etc, but so far i like 1.1.0. very much.
On my test server I get the following error after upgrading nginx and have to recompile ‘ModSecurity-nginx’ before restarting nginx.
$> service nginx configtest
nginx: [emerg] module "/etc/nginx/modules/ngx_http_modsecurity_module.so" version 1017006 instead of 1017008 in /etc/nginx/nginx.conf:8
Yes. Dynamic modules are sensitive bastards.
I will try to build it as standalone.
Unfortunately it won’t be easier  the compilation takes more time and it’s a bit more complex.
the compilation takes more time and it’s a bit more complex.
But don’t get discouraged, the process might have improved since I last played with it.
Let us know what you find
You were right. I spent several hours setting up the environment, required modules and compiling, but nginx hanged on start every time. I obviously missed something.
Your approach was rather quick and worked like a charm.
Now I really want to implement this in production, because not only it’s nice to see A+ rating test.vinsdigital.com now gets on immuniweb, looking at modsec_audit.log after just a few minutes of work freaked me out.
You can achieve auto update with nginx dynamic modules in Debian / Ubuntu by using 3 files
1, Script to install module,
2. A hook file in /etc/apt/apt.conf.d/ - to build and install dynamic modules before nginx upgrades
3. Worker script - to build scripts and pass error codes to apt hook
I have this working with 1 extra module and set the build path under /nginx/modules/ for now. You could add a copy option to move the files into that location once completed
Definately better then just putting nginx package on hold and forgeting I did that (and why). 
Mod security should really be a priority, to bolster security in general. You should see my server logs and how many malicious attacks the free OWASP rules trapped!
Combined with CSF, thankfully my servers have remained safe for many years.
Unfortunately my skill set doesn’t cover integrating with Hestia.
Is a recompile all that onerous? DirectAdmin for example needs rebuilds for the slightest change! I assume that you install ccache by default, as that helps considerably.
Any version of mod_sec and free OWASP rules is better than none at all. 
Including mod_sec/OWASP/CSF would make HestiaCP a much more viable replacement for CWP.
Any movement on this, guys?
We discussed it internaly and would love to implement it. Currently, we haven’t made any step forward due to other pending work.
Just a wee reminder, given a recent bad bot thread. 
Link to that thread pls
I think this one…
@eris got it in one. 
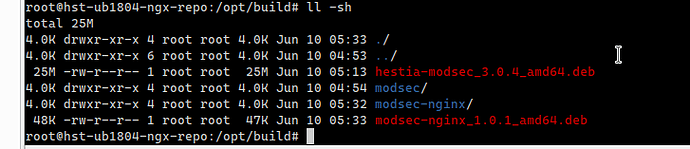
@AlwaysSkint I have started working on modsecurity for Hestia recently but unfortunately it will take some time before it’s released, it might not even end up there if I find any showstoppers.
Can you share the extra rulesets you mentioned on the other thead besides the default owasp ones?
TBH, in 30 years on *nix, I’ve never taken the time/effort to get to grips with regex. So, I end up appending to an existing rule, even though creating a custom one is much more appropriate.
In CWP I’d use these (haven’t got around to it ![]() )
)
/usr/local/apache/modsecurity-owasp-old/base_rules/modsecurity_crs_35_bad_robots.conf
/usr/local/apache/modsecurity-owasp-old/base_rulesmodsecurity_35_bad_robots.data
In WHM/cPanel ( OWASP ModSecurity Core Rule Set V3.0 ) I use the following
and append as follows (my emboldening of text):
SecRule HTTP_User-Agent “(?:\b(?:m(?:ozilla/4.0 (compatible)|etis)|webtrends security analyzer|pmafind)\b|n(?:-stealth|sauditor|essus|ikto)|b(?:lack ?widow|rutus|ilbo)|(?:jaascoi|paro)s|internet explorer|webinspect|.nasl|majestic|mj12bot|istellabot|baidu|yandex|ahrefs|VoilaBot|DotBot|spbot|grader|ezooms|seokicks|xovibot|semalt|semrush|LinksCrawler|aiHitBot|BUbiNG)”
“deny,log,auditlog,msg:‘Request Indicates a Security Scanner Scanned the Site’,id:‘1’,severity:‘2’”
The excellent configserver folks have a free modsec GUI for WHM/cPanel that might be useful to HestiaCP. The CWP GUI may also give you some ideas but is more basic.
Note that regardless of which ruleset is chosen, it can be necessary to define some rules as disabled or create exception based on a particular account/website. This is typical of Wordpress and some e-commerce packages, in addition to control panels. This can usually be handled within a GUI. Here’s a small sample:
CWP
SecRuleRemoveById 960017
Joomla
SecRuleRemoveById 960024
Wordpress
SecRuleRemoveById 981242
Drupal
SecRuleRemoveById 981231
PHPmyadmin
SecRuleRemoveById 981205
oscommerce
SecRuleRemoveById 959070
HTH.
Will you please share the script that you added in /etc/apt/apt.conf.d/? At present I am doing it manually but with automatic script will be helpful. At present I am using this script:
#!/bin/bash
command="nginx -v"
nginxv=$( ${command} 2>&1 )
nginxVersion=$(echo $nginxv | grep -o '[0-9.]*$')
echo version is http://nginx.org/download/$nginxVersion.tar.gz
wget http://nginx.org/download/nginx-$nginxVersion.tar.gz
tar -xvf nginx-$nginxVersion.tar.gz
cd nginx-$nginxVersion
./configure --with-compat --add-dynamic-module=../ModSecurity-nginx && make modules
rm -rf /etc/nginx/modules/ngx_http_modsecurity_module.so
cp -rf objs/ngx_http_modsecurity_module.so /etc/nginx/modules
service nginx restart
cd ../
rm -rf nginx-$nginxVersion.tar.gz nginx-$nginxVersion