I read here about implementing SFTP chroot jails. Where can we find more information about this feature and how we can use it?
Hi Felix
Sorry for the delay, we try usually to answer below 12hrs :).
SFTP is allowed by default for nologin users, it will also be enabled when you add a new user and also when you upgraded the system so 1.0.0.
Here you’ve the code reference inside the add user script: https://github.com/hestiacp/hestiacp/blob/fe045c5df2f5bd7d5e361029300900c41a43e63c/bin/v-add-user#L220
Thats was helpful
but the question for me is:
sftp is good because of encryption, but
with my sftp client i could see - not write - root and so on
with ftp the client does only see his home area
with sftp he can go up to root /
how can i adjust the behaviour same like ftp?
ok i see there is a vsftp configuration file. but help would be appreciated
Best regards Markus
Do you login as admin or as normal user? What usergroup you’ve set? Usually you need to have them on “nologin”, then they should be chrooted to the home directory.
i login as a normal user without special rights…
then i can connect with f.e. winscp to the home directory of that user and write and read
but i also can go up and read var, srv, bin etc inside root directory but not write
i can go inside other user directories but at
/home/someuser/web than reading is prohibited
thats ok so far
but is it neccessary that scp users can see root directory
with ftp going up is not possible
now i want to answer your question about the usergroup and nologin…
OK found the reason
“hosting package”
for short time i had hosting package default which was the only one i could use until you gave me the hint with thas ns1 ns2
i activated bash login for default
users which i had made with that could login via scp
but: when you remove bash login from already assigned default hosting package then users are not updated
the solution is:
if you set bash login inside hosting package , then users inside are not updated
you have to switch forward backward and then nologin is assigned as you have set inside the hosting package
i do not know if this behavior is intentional but i can live with that now
As already written: If you want to have jailed ssh, just give them nologin group. Bash is only if you need ssh access.
in addition to what @Raphael already said, a user that has normal shell access can see/read the filesystem when logging in with a normal shell anyway, so it would not make sense (even technically) to try and make sftp/winscp behave differently 
that’s why a jail only works for user which have no full shell access (aka nologin).
I’m dealing with this now as well. Not sure I understand the answer given? So I want to offer SFTP access to users,which are locked into their own /home/foo/ folder. Anything outside of that they can’t see.
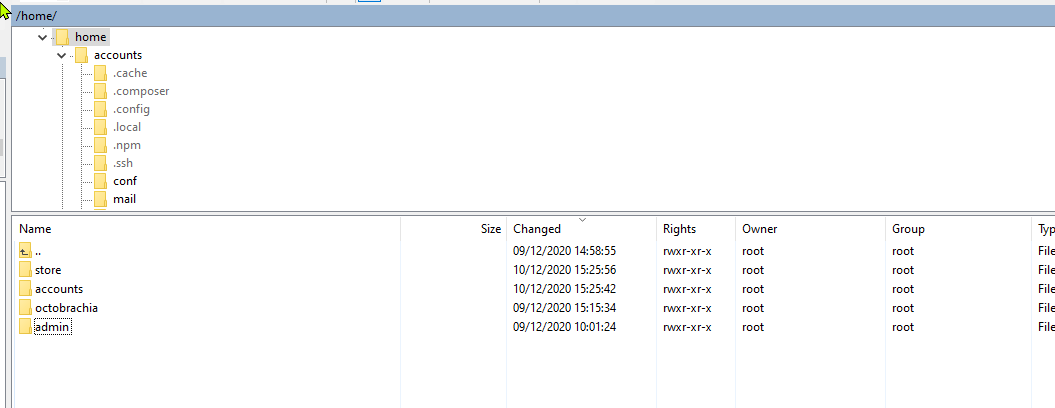
This is what I see when logged in as use “accounts”, with “bash” enabled:
On VestaCP there was a plugin you installed, and this allowed you to stop people going outside of their own jails. Is there no way to do that on here?
Thanks
Andy
Set shell to no login and it works fine…
It works at stopping me from moving in SFTP, but I still want SSH access for the user - but just limit them to their files/folders  (with nologin you obviously can’t login as SSH any more)
(with nologin you obviously can’t login as SSH any more)
Currently not possible we are working a solution for it in a future release
nice info and idea
can’t wait for it
thanks
My main use case is to move WordPress websites across servers. I perform this operation several times a week.
To export: I need to zip the wp-content and the database
To import: I need to copy 3GB zip files and extract them
ISSUES:
- The file manager can’t handle those sizes. I have already raised the max size.
- The file manager fails to unzip large files. Due to timeouts I suppose. It took like forever to perform the unzip and then the files were not unzipped.
- If I use nologin, then I can’t unizip with WinSCP
- If I use bash then there is no chroot.
I would love if you could come up with a solution. Maybe a WP-CLI script with wget / rsync.
I am not a programmer and I am afraid that my clumsy code would not meet any quality standard.
I do agree this are many situations that can benefits from a good ssh jail. In Debian 9 / Ubuntu 18.04 there was an option for RSSH how ever support for 20.04 / Debian 10 has dropped as the package wasn’t been updated for over x years.
Option would be replace it by GNU Rush. How ever setting it up is terrible…
Ah ok thats a shame. Well for now its not a major issue. Any of my friends I host I don’t give access to SSH anyway, but then that means we don’t get crontabs as well (I assume its the same as Vesta in that respect?)
You should still be able to use cronjobs via control pannel