Hi,
I am running HestiaCP v1.6.0
on ubuntu 20.04 dedicated sever.
It runs several wordpress websites.
It seems that HestiaCP is running Nginx as a reverse proxy in front of
the Apache webserver.
Since both nginx and Apache are on the same host and the host is secure, it’s a waste of resources to encrypt and decrypt using HTTPS between nginx and Apache. Can I just have nginx terminate the TLS and reverse proxy it to http://127.0.0.1:8080 using just plain HTTP
That way I don’t need the certificates for the apache.
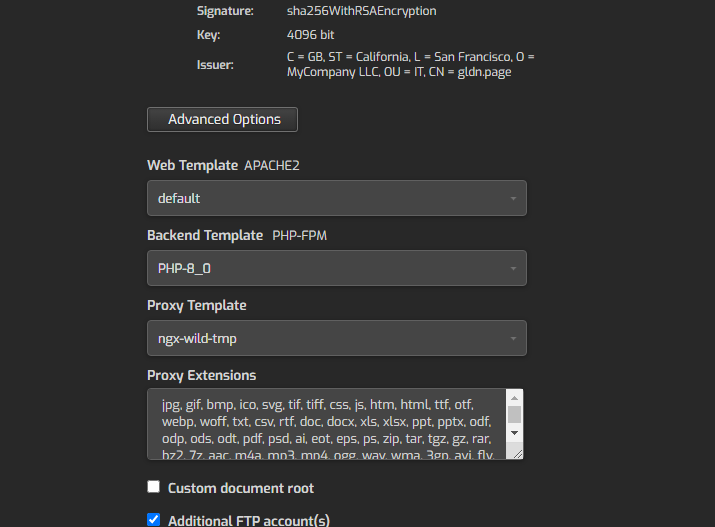
So - I could create custom templates :
First the port 80 one on nginx - just forcing HTTPS
server {
listen %ip%:%proxy_port%;
server_name %domain_idn% %alias_idn%;
include %home%/%user%/conf/web/%domain%/nginx.forcessl.conf*;
//// THE LINE ABOVE uses a 301 redirect to https so everything below is ignored ////
location / {
proxy_pass http://%ip%:%web_port%;
location ~* ^.+\.(%proxy_extensions%)$ {
root %docroot%;
access_log /var/log/%web_system%/domains/%domain%.log combined;
access_log /var/log/%web_system%/domains/%domain%.bytes bytes;
expires max;
try_files $uri @fallback;
}
}
location /error/ {
alias %home%/%user%/web/%domain%/document_errors/;
}
location @fallback {
proxy_pass http://%ip%:%web_port%;
}
location ~ /\.(?!well-known\/|file) {
deny all;
return 404;
}
include %home%/%user%/conf/web/%domain%/nginx.conf_*;
}
Now for the port 443 on nginx - a custom template using SL certificates
server {
listen %ip%:%proxy_ssl_port% ssl http2;
server_name %domain_idn% %alias_idn%;
ssl_certificate /etc/letsencrypt/live/%domain%/cert.pem;
ssl_certificate_key /etc/letsencrypt/live/%domain%/privkey.pem;
ssl_stapling on;
ssl_stapling_verify on;
error_log /var/log/%web_system%/domains/%domain%.error.log error;
include %home%/%user%/conf/web/%domain%/nginx.hsts.conf*;
location / {
proxy_pass http://127.0.0.1:8080;
location ~* ^.+\.(%proxy_extensions%)$ {
root %sdocroot%;
access_log /var/log/%web_system%/domains/%domain%.log combined;
access_log /var/log/%web_system%/domains/%domain%.bytes bytes;
expires max;
try_files $uri @fallback;
}
}
location /error/ {
alias %home%/%user%/web/%domain%/document_errors/;
}
location @fallback {
proxy_pass https://%ip%:%web_ssl_port%;
}
location ~ /\.(?!well-known\/|file) {
deny all;
return 404;
}
proxy_hide_header Upgrade;
include %home%/%user%/conf/web/%domain%/nginx.ssl.conf_*;
}
And a custom template for apache2
<VirtualHost 127.0.0.1:8080>
ServerName %domain_idn%
%alias_string%
ServerAdmin %email%
DocumentRoot %docroot%
ScriptAlias /cgi-bin/ %home%/%user%/web/%domain%/cgi-bin/
Alias /vstats/ %home%/%user%/web/%domain%/stats/
Alias /error/ %home%/%user%/web/%domain%/document_errors/
#SuexecUserGroup %user% %group%
CustomLog /var/log/%web_system%/domains/%domain%.bytes bytes
CustomLog /var/log/%web_system%/domains/%domain%.log combined
ErrorLog /var/log/%web_system%/domains/%domain%.error.log
IncludeOptional %home%/%user%/conf/web/%domain%/apache2.forcessl.conf*
<Directory %home%/%user%/web/%domain%/stats>
AllowOverride All
</Directory>
<Directory %sdocroot%>
AllowOverride All
Options +Includes -Indexes +ExecCGI
</Directory>
<FilesMatch \.php$>
SetHandler "proxy:%backend_lsnr%|fcgi://localhost"
</FilesMatch>
SetEnvIf Authorization .+ HTTP_AUTHORIZATION=$0
IncludeOptional %home%/%user%/conf/web/%domain%/%web_system%.conf_*
IncludeOptional /etc/apache2/conf.d/*.inc
</VirtualHost>
Does seem practical ?
It would mean less work/time encrypting/decrypting between servers
on the same host.
Thanks